Cybersecurity Maturity Model Certification (CMMC) Advisory & Readiness Services
Why CMMC Still Matters
CMMC requirements continue to evolve, but DoD contractors are still expected to protect controlled unclassified information (CUI) and demonstrate strong cybersecurity practices. Waiting for final rulemaking increases the risk of non-compliance, data exposure, and contract disruption.
Even though CMMC 2.0 timelines have shifted, the underlying expectation has not: you should be implementing and maintaining a mature, documented cybersecurity program today.
What Changed With CMMC 2.0?
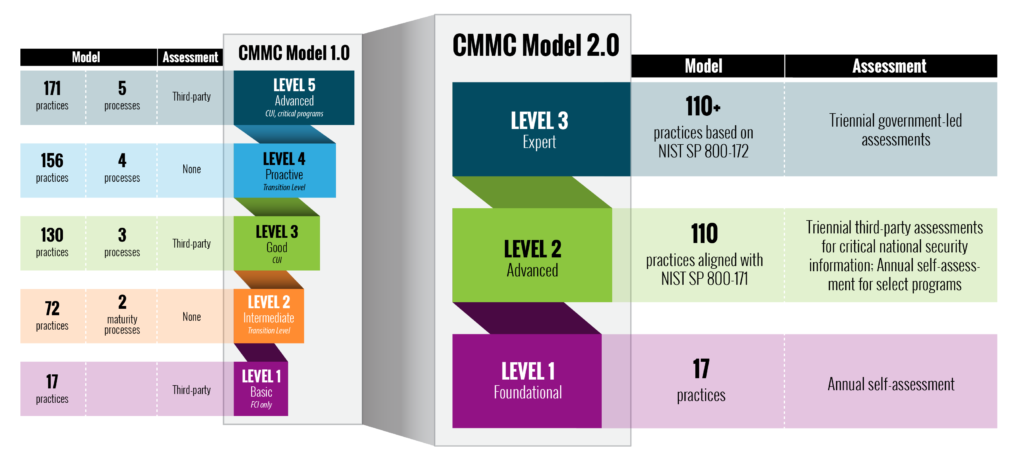
CMMC 2.0 streamlines the original model while introducing a more flexible path to compliance. Although details are still being finalized, several core themes are clear:
-
Fewer certification levels, focused on practical implementation of NIST-aligned controls.
-
A smaller subset of organizations requiring third-party certification, with more opportunities for self-assessment in lower-risk cases.
-
Strong continued emphasis on protecting CUI, incident response, and continuous improvement.
These changes do not reduce the need for strong cybersecurity; they sharpen the focus on measurable, evidence-backed controls. The graphic below highlights the basic differences between the original model and Model 2.0.
 Source: dodcio.defense.gov/CMMC/
Source: dodcio.defense.gov/CMMC/
CMMC certification requirements continue to be a moving target and the most current CMMC information can be found on the U.S. Department of Defense website by following the links below.
The main page for CMMC Model 2.0 information can be found here.
JANUS will be one of the approved organizations to help you achieve CMMC Model 2.0 certification when the program is finalized, and certification is possible. We can help you protect your operations and infrastructure now while preparing for the future.
To find out more about FAQs involving the CMMC model, click here.
Ready to assess your CMMC readiness? Request a complimentary consultation and a JANUS CMMC expert will contact you.
